As more and more users seek better protection for their private data across the technological space, Google has continued to introduce additional features in Android for their more privacy minded consumers.
Notably, Google introduced full disk encryption (FDE) in Android Lollipop and made it a requirement for any device shipping with Android Marshmallow to have FDE active. But despite these improvements, there has been one issue that many security buffs have scoffed at for years: the inability to use a secure encryption password.
Okay, I may have exaggerated a bit there. It's not as if you can't set a really secure encryption password, but due to the fact that your encryption password is (partly) tied to your lock screen password you would have to burden yourself with entering a really difficult password every time you wanted to use your phone. For the true security buff, this would be seen as a necessary sacrifice to be made, but for the less devoted the massive inconvenience is undesirable. What about using your fingerprint, then? Let's just say someone interested in keeping their private data out of the eyes out of the reach of the government probably doesn't think too highly of biometric authentication, at least for the time being.
So how, exactly, are we supposed to decouple our encryption password from our (often) short lock screen password (and thus, susceptible to brute force attacks)? Certain custom ROMs such as the security-focused Copperhead OS allow you to set a separate encryption and lock screen password, but what about users who don't have a Copperhead OS supported device?
Interfacing with Cryptfs
Thankfully we can use the same commands that Android uses internally to change your encryption password. These commands are defined in the cryptfs.c file which contains the encryption file system implementation used in AOSP.
Disclaimer: if you choose to use the method described below to change your encryption password, you are doing so at your own risk. Certain vendors such as LG or custom ROMs such as CM13 have slightly modified the syntax required to use cryptfs, so you will need to adjust and use the correct syntax. More details here. Forgetting your password means you will be completely locked out of your device if you reboot.
If you have root access on your device, or at least a way with which you can temporarily achieve root access, then you will need to enter one of the following commands into the shell terminal emulator.
If you are on a version of Android prior to 5.0 Lollipop, then enter the following command:
vdc cryptfs changepw <yournewpass>
For users on Android 5.X Lollipop:
vdc cryptfs changepw password <yournewpass in hexadecimal>
For users on Android 6.X Marshmallow:
vdc cryptfs changepw password <yournewpass>
You can verify your new password (or check your old password) by entering this command:
vdc cryptfs verifypw <yourpass>
If you see a code number '200' returned in the terminal output then you correctly entered the currently-set encryption password. Note: if you are currently using a pattern lock for your password, then when you are entering your password here you will need to translate each of the pattern dots into a number (think of the dot pattern as a T9 dialer, so the top-left dot correlates to a 1 and the bottom-right dot correlates to a 9).
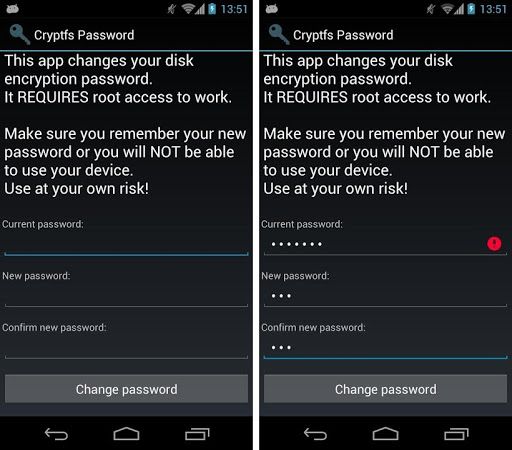
If you would rather have a graphical interface to change your encryption password, you can use this app on the Play Store. Worried about any potential security issues with this app? No problem, since it's open source you can compile the app yourself by using the source linked in the app's description.
For a (very, very thorough and technical) explanation behind the evolution of encryption with each iteration of Android you can read through this excellent post.