latest

How to lock apps on your Android phone to prevent unauthorized access
Lock your apps to keep your data safe from prying eyes.
Smartphones are a big part of our lives today, and the best smartphones serve as more than just phones. They hold memories like photos and videos but also protect other important things, like passwords and confidential apps. Many of us have banking apps or investing apps on our phones, and allowing the wrong person access to those apps could be detrimental to our online security portfolio. Luckily, there are steps you can take to secure applications on the best Android phones, including locking applications individually.

Why home cybersecurity is important
Keeping yourself safe from online threats is more important than ever.
Our lives are more and more online than ever, and the wealth of security threats online is only increasing. It's important to protect yourself online, and with a few easy steps and some simple considerations, you can vastly decrease your chances of being exploited. We'll examine what features protect your home network from cybersecurity attacks, where some of the weak points are, and what you can do to ensure you're not one of the unfortunate few who are left picking their lives back up after being compromised.
Microsoft discovers XZ Utils backdoor vulnerability in Linux distros, issues guidance
A Microsoft employee came across a very dangerous backdoor exploit in XZ Utils, affecting numerous Linux distros; the company has now issued guidance.
A few days ago, we learned that the Python Package Index (PyPI) has temporarily restricted the creation of new accounts and package submissions to its portal following the emergence of a malware campaign through which attackers were uploading malicious packages to the directory in a coordinated manner. Now, Microsoft has detailed a new vulnerability in Linux distributions after it was discovered recently by a company employee.

The official Python package repository has blocked new registrations in response to latest malware campaign
The official third-party package repo for Python, PyPI, has blocked new project and user creations in response to a sophisticated malware campaign.
If you utilize Python as a programming language during software development activities, you might know about Python Package Index (PyPI). This is the official repository for Python packages and is essentially the place where pandas, numpy, seaborn, matplotlib, and other libraries are downloaded from when you run pip install libraryname. Now, in a move that may surprise many, PyPI has blocked new user registrations in an attempt to defend itself against a recent malware campaign.

Microsoft’s patch for a big Windows 10 BitLocker vulnerability is a dud
Windows 10 users are waiting for Microsoft to roll out a more seamless update
If you have a Windows PC, you know the importance of keeping up to date with the latest patches from Microsoft. Doing so can help ensure that your device is as secure as possible against evolving threats. However, you might hit a snag in your efforts if the patch can’t be seamlessly installed onto your PC. This is what some Windows 10 users are now facing following the release of a patch from Microsoft, created upon the discovery of a BitLocker encryption bypass vulnerability.
Future Intel, AMD, and Arm CPUs could be impacted by a major security flaw
The vulnerability could leak users’ passwords and other data to bad actors
When you choose to purchase a new CPU, you might assume that you’re getting a product with the latest features to protect against hacking vulnerabilities. That being said, some bugs go unnoticed until they become problems for users. Thankfully, there are researchers who look into potential security issues before they have a chance to do significant damage. New data from the Systems and Network Security Group (VUSec) at Vrije Universiteit Amsterdam has done just that, and their findings are raising eyebrows over upcoming CPUs.

Microsoft’s Windows Hello fingerprint authentication bypassed on Dell, Lenovo, and Surface laptops
If you've heard that researchers bypassed Windows Hello on Dell, Lenovo, and Surface laptops, this is everything you need to know.
If you have a Windows laptop, then you probably have come across Windows Hello. It's a biometric login that on supported laptops, allows users to login with either a facial scan, an iris scan, or a fingerprint scan. In the case of using a fingerprint to get into your laptop, though, be warned: researchers from Blackwing HQ have bypassed Windows Hello on three different laptops from Dell, Lenovo, and Microsoft.
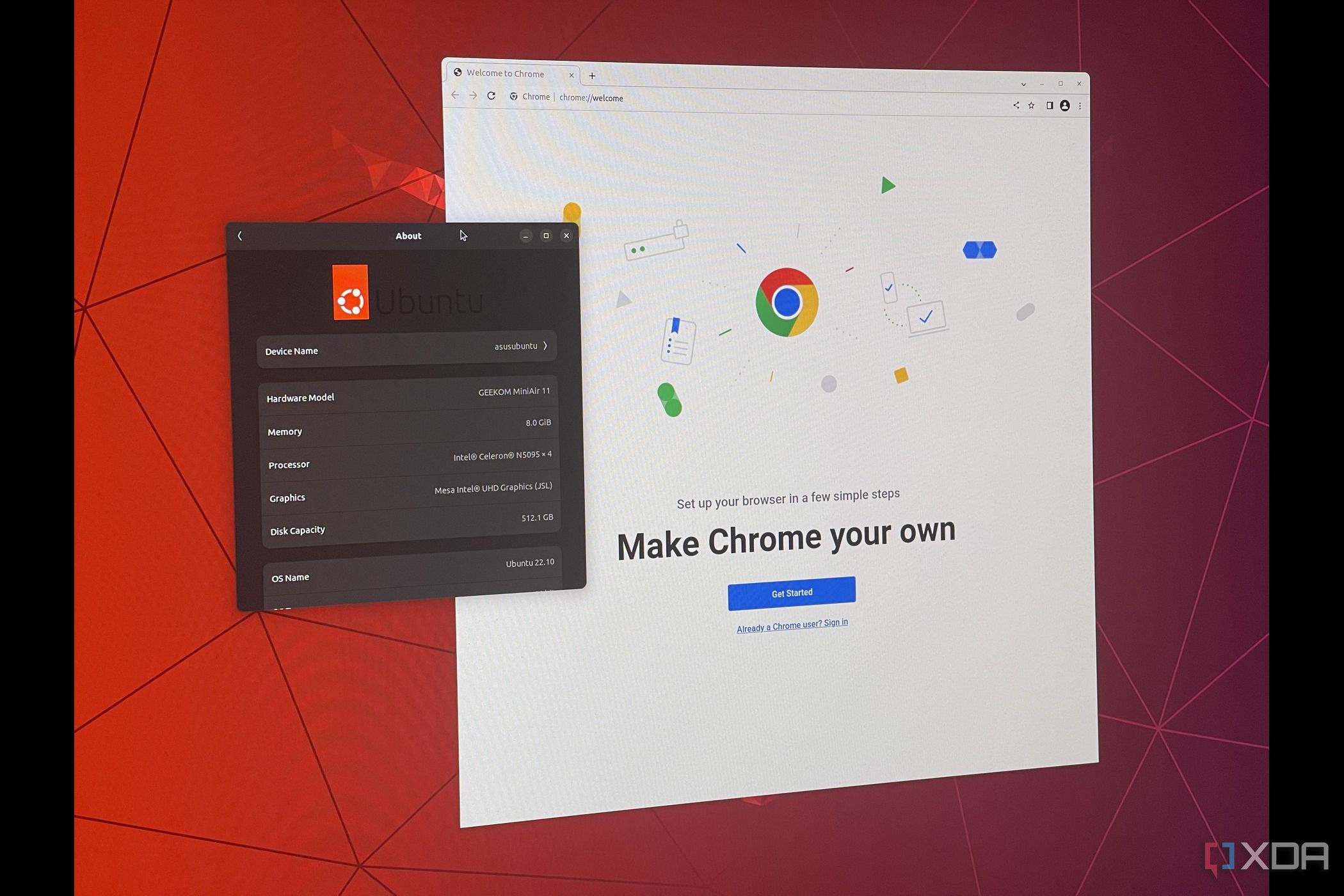
How to change password on Ubuntu Linux
Looking to change your old password on Ubuntu? It's easy to do so through the terminal.
Ubuntu Linux isn't the most popular desktop operating system out there, but there are a lot of valid reasons as to why a large crowd of people prefers it over macOS or Windows. It's free and open source, offers plenty of distributions with different features and interfaces, and it's getting quite good for gaming as well. With that said, there's definitely a learning curve when you're switching over from a Mac or Windows PC. Even trivial things such as changing your password can get a bit complicated.

Can't miss deal knocks 50% off this popular Arlo security bundle
A must-have if you're looking to protect your home or office.
The Arlo Pro 4 Spotlight Camera Security Bundle comes with everything you'll ever need to keep your home or office secure. The kit comes with three camera that can be mounted anywhere, rechargeable batteries for quick and easy replacement, anti-theft mounts, and a sign that lets those around you know that your place is being monitored by Arlo cameras. While this kit typically costs quite a bit coming in at $600, it's now on sale, with a discount that knocks 50% off. That means, for a limited time, you can score this security bundle for just $300 while the deal lasts.

Early Black Friday deal knocks 61% off this Blink security camera bundle for Prime members
A fantastic camera bundle that's now more affordable than ever with a recent price drop of $220 for Prime members.
If you're looking to get serious about security in your home or office, look no further than this Blink Outdoor 4 bundle that's now 61% off for Amazon Prime members. This bundle not only includes two Blink Outdoor 4 cameras, but it also comes with a floodlight camera as well, along with a camera that can be used indoors that can cover a wide area of space thanks to its pan and tilt features.

Massive price drop knocks 50% off this Blink outdoor wireless camera 3-pack bundle
My Best Buy members can save an additional $25 off, bringing the price down even further in this fantastic deal.
If you're looking for a great way to monitor your home or office, this three-camera bundle from Blink is going to be an excellent option. It's easy to set up, can cover a large span of space and is now quite affordable at a price of just $125 for a limited time. My Best Buy members will be able to save just a touch more with an extra $25 off the already reduced price, bringing the three-camera bundle down to just $100.

Fire TV Stick 4K Max and Blink Video Doorbell bundle now 46% off in Prime member exclusive flash deal
This limited-time deal is the perfect way to add some smarts to your home and do so at a reasonable price.
We're finally heading into the holiday shopping season and as you might expect, both Best Buy and Amazon have already started offering plenty of discounts on some of its most popular products. While we're still weeks out from Black Friday, Amazon's dropped a fantastic deal that bundles its Fire Stick 4K Max with a Blink Video Doorbell. This bundle would normally retail for $120, but is now priced well below that at 46% off, coming in at just $65 for a limited time for Amazon Prime members.
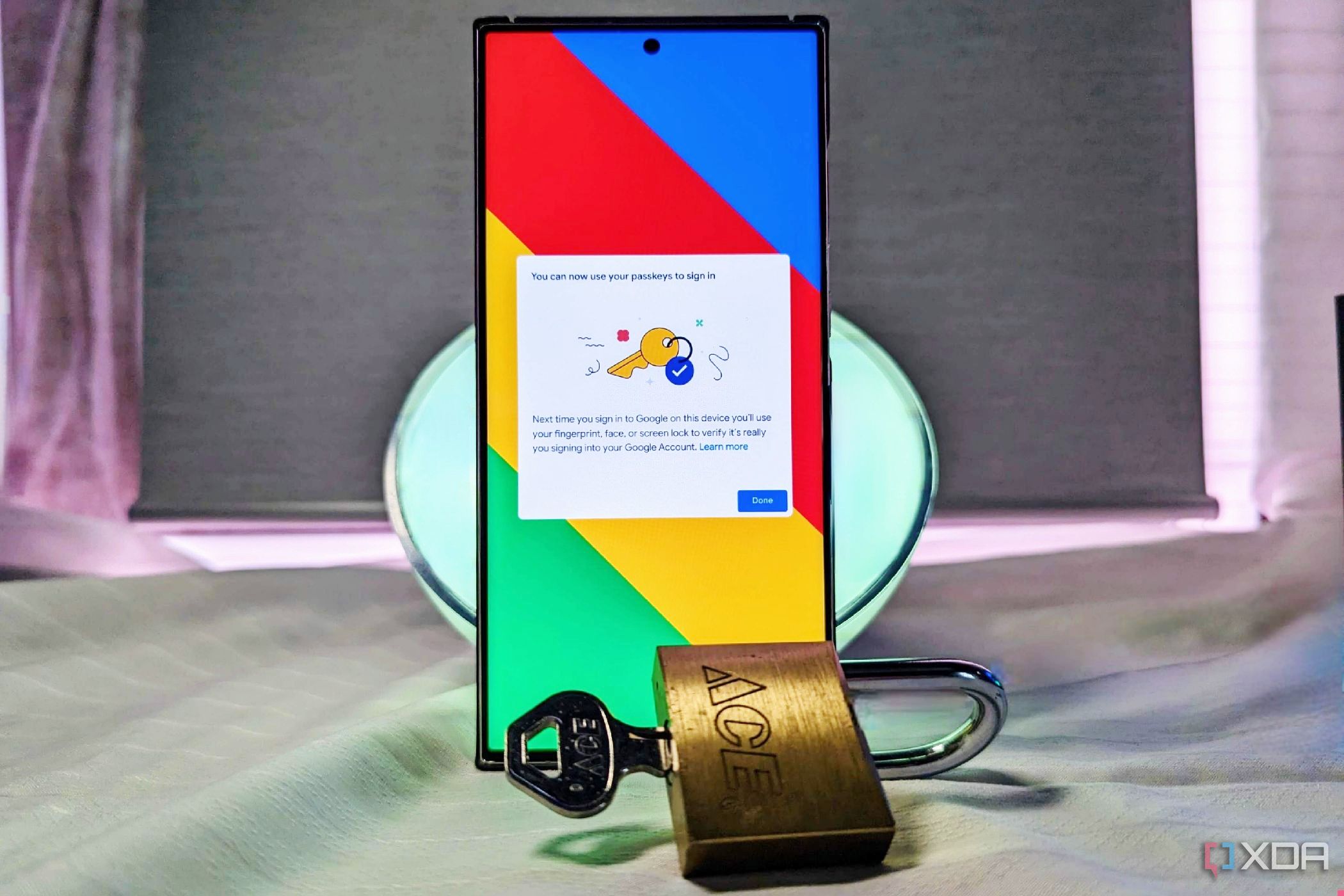
How to set up a passkey for Google
A cybersecurity dream has been to create a world without passwords, and we're one step closer to that vision with Google passkeys.
Google has said for some time that it believes the future of online security is with passkeys, which replace traditional alphanumeric passwords. It added support for passkeys across Google services earlier this year, but now, it's positioning passkeys as the default login method for personal Google accounts. Since it's nearly impossible to remember all those passwords yourself, so most people end up using the same password across many accounts or utilizing the best password managers. Starting Oct. 10, 2022, Google began prompting users to create and use passkeys by default, ditching their password. If you're curious what this all means for your sign-in process, or how to create a passkey, you're in the right place.
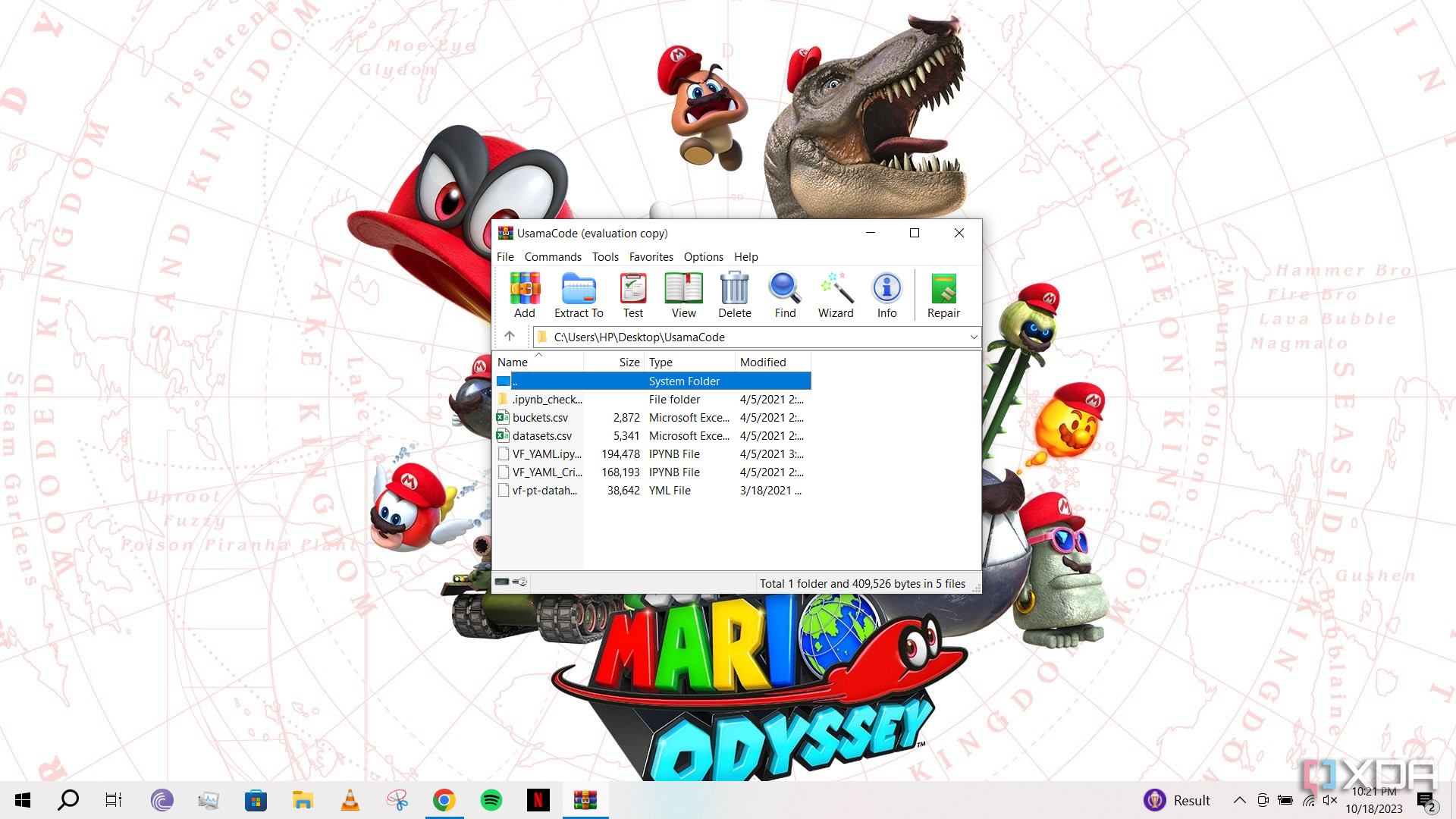
WinRAR has a major security vulnerability, manually update now
A WinRAR vulnerability is being widely exploited because the archiving utility does not allow automatically updating to a patched version.
WinRAR is one of the most used compression utilities out there, although Windows 11 might be looking to make a dent in its popularity with native support for 7Z, RAR, and TAR.GZ formats. However, those who leverage WinRAR may want to update the software as soon as possible as a security vulnerability is reportedly being exploited by certain state-sponsored actors.
Google is making it easier to protect your privacy online
Google will now allow you to quickly delete the last 15 minutes of your browsing data through the three-dot menu.
Cybersecurity Awareness Month has been celebrated in October for the past couple of decades in the United States. Big tech firms typically announce new security features for their software and hardware during this month as a way to increase awareness of the topic and also offer more ways to enhance security on your everyday devices. Google has now announced a bunch of capabilities that it is working on in order to protect your security and privacy in online environments.

My favorite indoor security camera from Eufy is now down to its lowest price ever in this Prime Day deal
Eufy's indoor pan and tilt camera provides excellent image quality and is ultra-responsive when it comes to detection.
There are a large number of security cameras available, and each have their strengths and weaknesses. If you're looking for a high-quality camera that can outperform most of the competition, but still comes in at an affordable price — look no further than my favorite Eufy camera that's now priced well below retail, coming in at just $36 for a limited time during Amazon's Prime Big Deal Days sales event.

Save 50% on Blink Outdoor 4 camera bundles with these early Prime Day deals
Fantastic deals on Blink camera bundles that can keep your home or office secure.
This is one of the best security camera systems you'll find that's not going to break the bank. With Amazon's Blink camera system, you're going to get a reliable system, with cameras that can shoot great quality 1080p video during the day and night. The cameras feature enhanced motion detection, so you can be alerted whenever there's a person moving about or a package is being dropped off.

Early Prime Day deal knocks 50% off this Blink Video Doorbell camera bundle
An excellent and affordable bundle for anyone who's trying to secure their home or office space.
Don't miss out on this deal that knocks 50% off this Ring Video Doorbell camera bundle for a limited time. This is the combo you want if you're looking to monitor your home or office at an affordable price. While this set normally comes priced at $130, during this limited time promotion ahead of Prime Day, you can score this bundle for just $65, which is an absolute steal.

Everything you need to know about CPU vulnerabilities like Zenbleed, Downfall, Inception, and more
CPU vulnerabilities have been all the rage recently, with Zenbleed and Downfall being two recent ones. But how worried should you be?
CPU vulnerabilities have been in and out of the news in recent years, and they often come with a pretty scary message when it comes to them being disclosed. In the case of Zenbleed and Downfall, it was that any application on your computer could access the memory of any other program running under the right circumstances. Sounds intense, right?
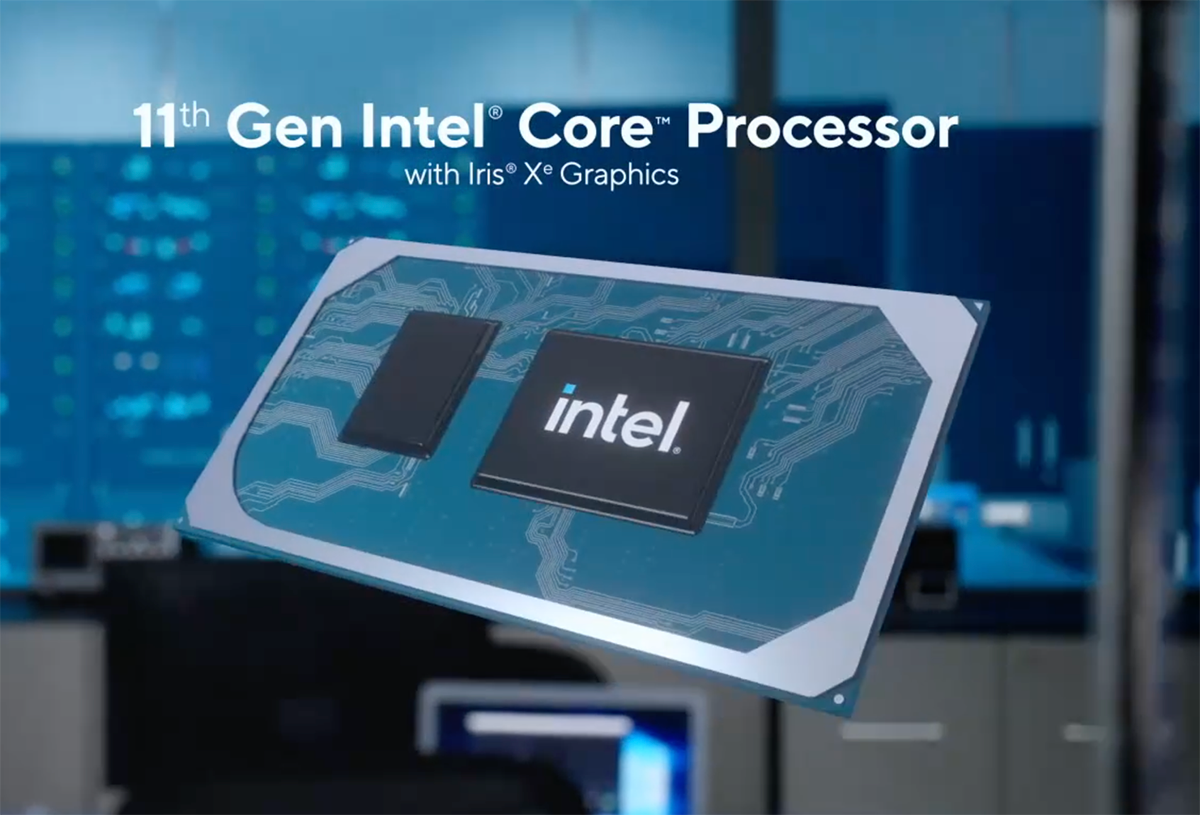
Intel Downfall attack: What we know about this CPU flaw
With CPU exploits all the rage recently, one pretty severe one affects a ton of Intel processors.
With Zenbleed and Inception affecting AMD when it comes to CPU exploits recently, Intel hasn't come out unscathed. Downfall is a new CPU vulnerability that Intel has disclosed, which uses Gather Data Sampling in order to extract data and other sensitive information on a number of CPUs. These CPUs include ones from Intel's Skylane through to Rocket Lake and Tiger Lake.








