
Best Google Pixel 7a cases in 2024
Keep your Google Pixel 7a safe with these durable protective cases.

Keep your Google Pixel 7a safe with these durable protective cases.
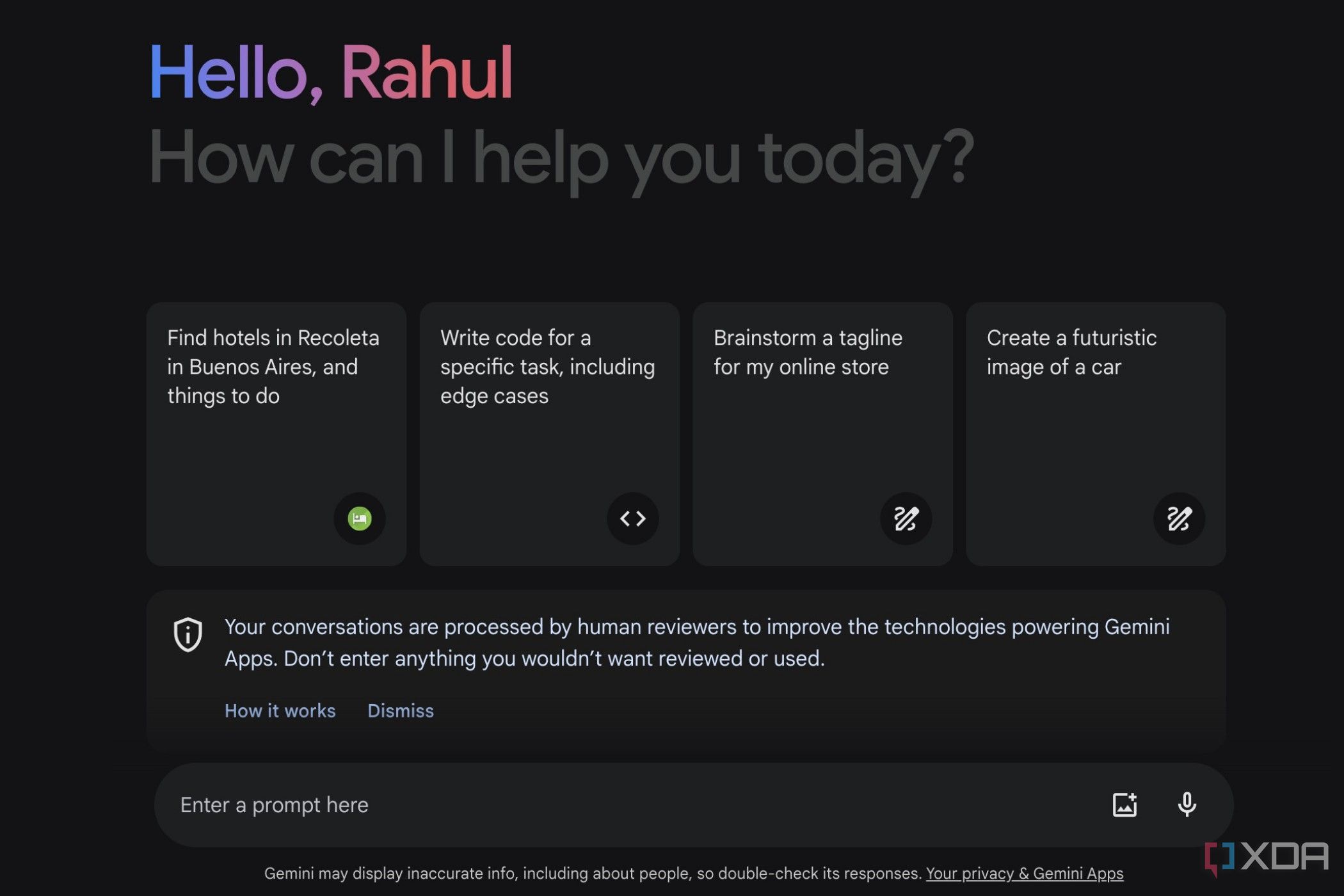
Google Chrome's upcoming feature will make chat with Gemini super simple.
A few months ago, Google made a lot of changes to its AI strategy, including introducing a new mobile app, renaming Bard to Gemini, a new subscription tier, and more. It also has many exciting announcements regarding Gemini planned for the future. One of the noteworthy features Google is currently working on is Gemini integration for Google Chrome desktop.

Give your eyes a rest when browsing Google Chrome using Dark mode.
Many people look at screens for hours on end. It doesn’t matter if someone uses a screen to code a program or watch tutorial videos; by the end of the day, users generally need to rest their eyes. If you are one of these people but still need to look at screens, Google Chrome’s Dark mode comes in handy.

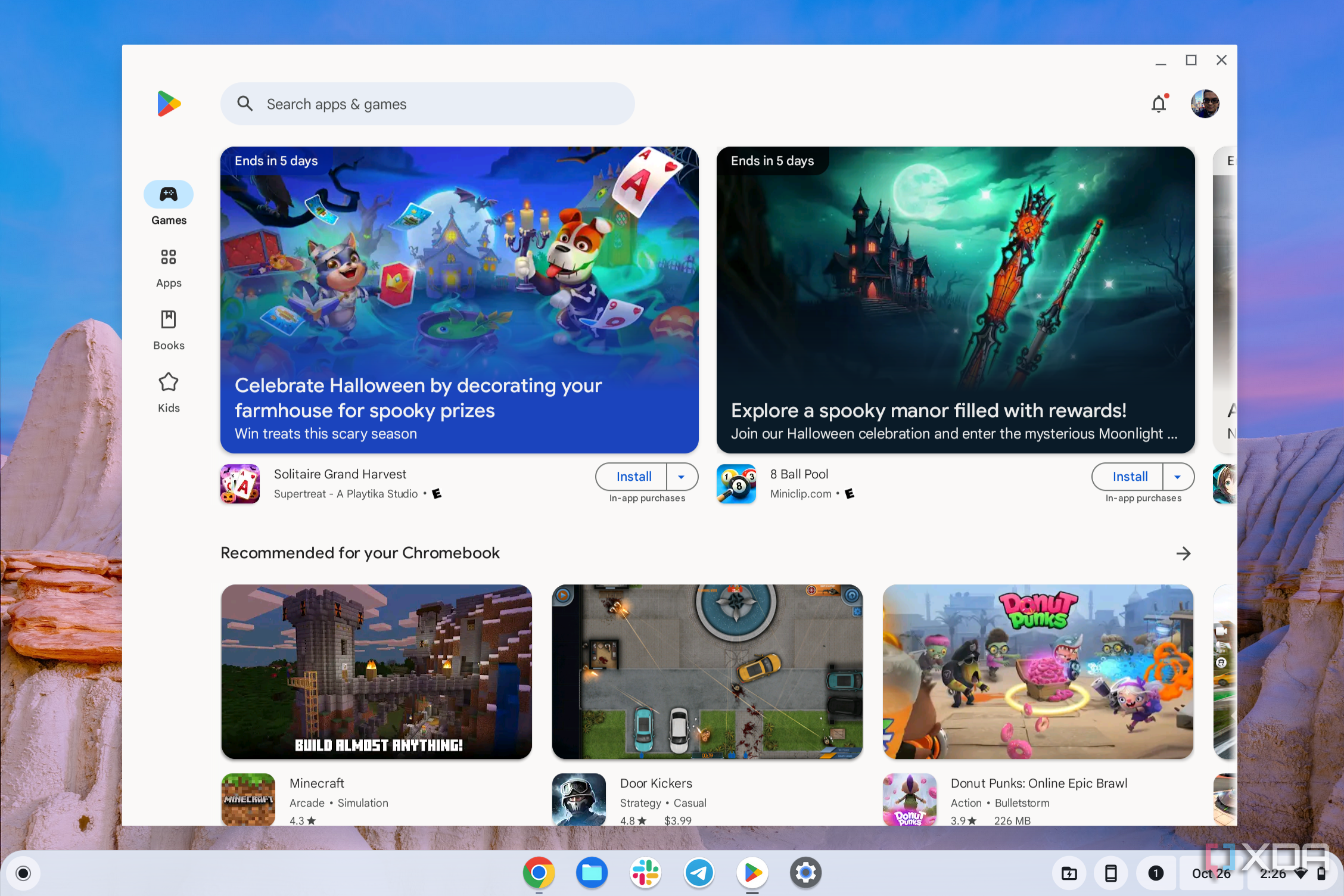
Want to use an app on your Chromebook that isn't on the Google Play Store? You can sideload it!
Apart from browsing the web via Google Chrome, your Chromebook can also run Linux and Android apps. While most Android apps are available in the Google Play Store, you also have the option to sideload apps that aren't accessible from the official Play Store. Sideloading apps with ChromeOS does require some effort though. You need to enable developer mode on your Chromebook or use ADB (Android Debug Bridge) to complete the job.

Google is notorious for killing off products just a short time after launch, with many arguing that the company does not give new services a proper chance to grow. A prime example of this is Stadia, which lived just from 2019 to 2023, despite the firm pitching it as a premier solution to play AAA games via the cloud. Now, another Google service is receiving similar treatment, less than four years after inception.
Google shows signs of wanting to replace Assistant with Gemini, but is it all good news?
A few days ago, people found some interesting text while digging through the APK files for the Google app on mobile devices. This text alluded to Google's AI assistant, Gemini, coming to Android tablets. However, unlike smartphones that can download Gemini as a separate app, the text implies that Google Gemini will instead be built directly into the Google app. The text went on to explain that users will have the chance to choose between using Google Gemini or Assistant to help them with their on-device tasks, but the way it was worded implied that the company would eventually replace Assistant with Gemini.
ChromeOS 123 is now being rolled out with some handy new customization options.
Google has started rolling out the ChromeOS 123 update to the Stable Channel, adding some noteworthy customization options. From allowing you to customize keyboard shortcuts to completing actions with the click of a button, the latest ChromeOS update can save you time and effort in performing some of your routine tasks.

Do you remember when Google came under fire for how it presented Incognito mode? If you didn't catch the news, Google came under fire after people accused the tech company of not accurately describing what Incognito mode does. As part of the lawsuit, Google changed how Incognito mode is worded to better reflect what it does. Now the company is going even further by erasing all browsing data gathered from Incognito mode users since 2016.

These are some of the best deals you're going to find on the Google Pixel Fold so don't miss out.
The Pixel Fold is still one of the best foldable phones of 2024 and for good reasons. One of the phone's main highlights is its excellent design, which allows it to take the crown as one of our favorite book-style foldables, sitting perfectly in the hand for hours of comfortable use. In addition, it has great software, a powerful processor, and excellent cameras. Of course, foldable phones are never cheap, and the Pixel Fold is no exception here with a starting price set at $1,799.

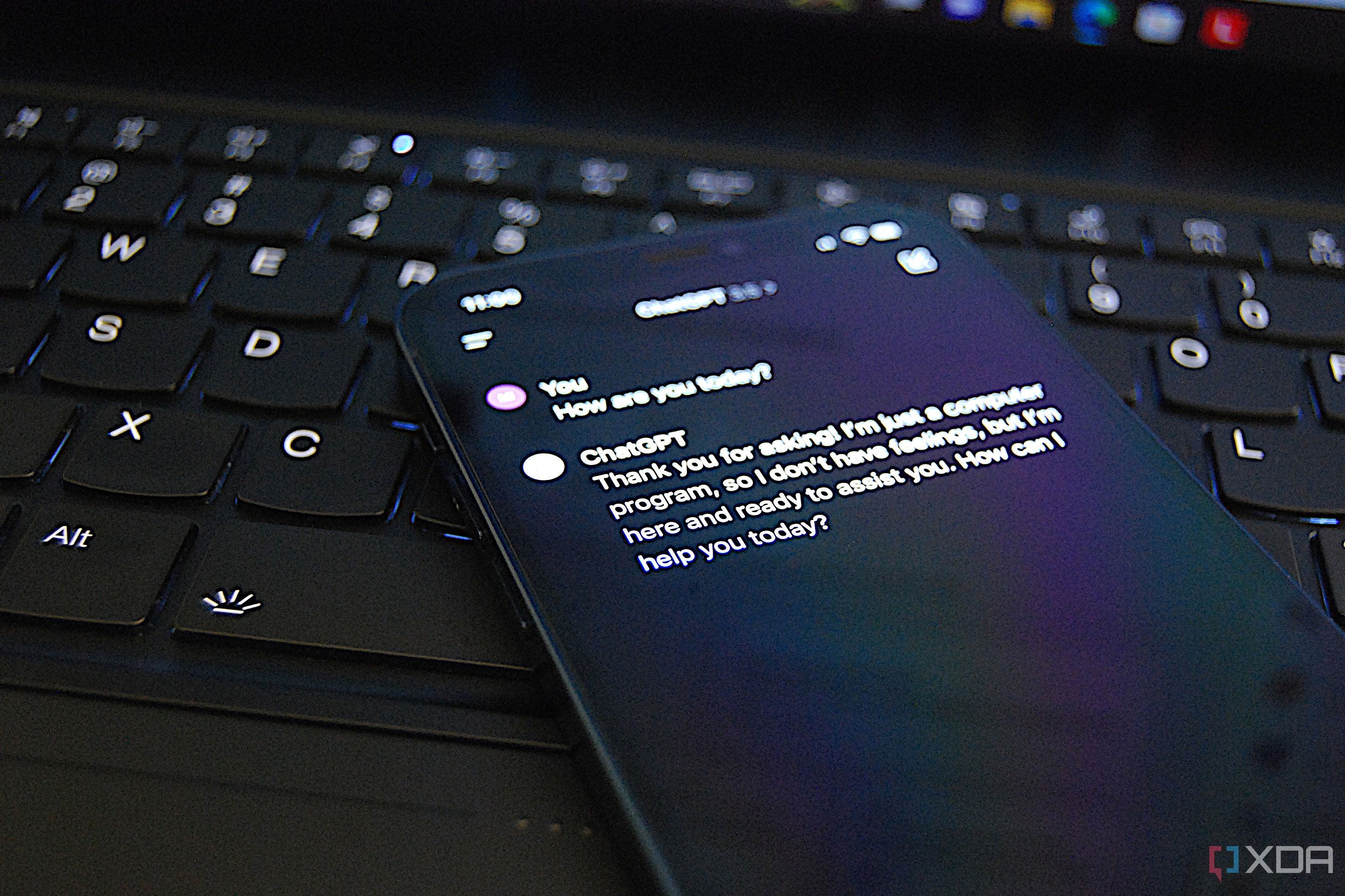
LLMs like ChatGPT, Gemini, and Copilot no longer impress nearly as much, but I'm hopeful they'll be able to do a lot more in the future.
The world of large language models has been slowly ticking along with new improvements and changes over time. We've seen iterations of GPT-4 come as OpenAI continues to improve the model, and advancements like Retrieval-Augmented Generation (RAG) have started to power local solutions like Chat with RTX. There's a lot more that could be happening in the world of language models though, and these are the things that we'd love to see next.

In order for Google to personalize ads for you, it has to know as much as it can about you.
The internet is a ubiquitous part of modern life, almost to the point of necessity. You can use the World Wide Web to watch movies and listen to music via streaming services, play tabletop RPGs remotely, and even learn how to repair Windows 11 computer glitches. However, one of the most popular uses of the internet is online shopping. Why brave a Black Friday sale in-store when you can purchase discounted items from the safety of your laptop?

Got a Windows on Arm PC? You can finally use Chrome comfortably
After roughly seven years of Windows on Arm PCs being on the market, Google is finally releasing a version of Chrome that's optimized for them. The native browser has been available in the Canary channel since January.
Apple's track record with AI and ML in Siri doesn't mode well for the future. Outsourcing to a company like Google or OpenAI is a far better solution.
Artificial intelligence is part of the conversation when talking about virtually all parts of the tech industry in 2024. Despite that being the case, Apple has been relatively quiet on the AI/ML front. This is all while competitors like OpenAI, Google, and Microsoft are racing to ship AI products. In fact, although the measure did not pass, 37.5% of Apple shareholders voted in favor of conducting a report concerning the company's AI efforts. People are concerned that Apple may be asleep at the wheel when it comes to AI, but that isn't exactly the case. Apple CEO Tim Cook has been steadfast in his claim that the company will ship AI features on the iPhone 16 series later this year. To do so, Apple might follow an old adage: if you can't beat 'em, join 'em.
Claude 3 Opus is a groundbreaking new AI model that manages to really impress.
In the world of large language models, it's been dominated by ChatGPT, Microsoft Copilot, and Google Gemini. If you've heard of Anthropic, its new LLM dubbed "Claude" has been doing rounds as a potential major competitor in the space. Claude 3 Opus recently launched, and it's managed to really, really impress. This is how it stacks up against Google Gemini Advanced in particular.

Android 15's second developer preview definitely feels bigger than the first.
Android 15 had its first developer preview arrive a little while ago, and with it came features and improvements that were rather small in scope but still managed to improve quality of life significantly. That's the case with Android 15 Developer Preview 2 as well, though there's arguably more inside than in the first devleoper preview. Plus, that's without even getting into all of the under-the-hood changes that are probably there too.

Google's newest Pixel 8 Pro looks to be a great smartphone, but you'll want to keep it safe with these amazing cases.
The Google Pixel 8 Pro debuted in October 2023 and has since maintained its spot as one of the best smartphones on the market in terms of design, functionality, and camera versatility. While it did get a price bump, there's no denying that it's still a great-value Pixel and one of the top Android phones you can get, especially now that Google is offering seven years of software and security updates. However, what Google isn't giving you is a case, and you'll want to pick up one for your Pixel 8 Pro as soon as you get it. Whether you're looking for protection, style, or something else altogether, the cases we've listed below have got you covered.

Avoiding phishing attacks just got easier.
Oftentimes, your browser is the first point of defense between your PC and the viruses strewn across the internet. There are other ways you can catch a nasty computer virus, but for the most part, clicking a shady download link or falling for a convincing phishing email are the main ways people end up with something bad on their system.

Here are all the options for running Steam on your Chromebook for gaming.
Steam is one of the most popular gaming platforms on the Windows, Mac, and Linux operating systems. If you recently purchased a new Chromebook, you might feel a bit excluded from the gaming party, but it turns out there are actually several methods to run Steam on ChromeOS. In fact, Google and Steam partnered together to make it possible to run Steam on ChromeOS through the Beta channel. There are also some other ways to get Steam games on your Chromebook, which we'll cover in this guide.

In this tutorial we demonstrate how to enable developer mode in ChromeOS. This is very useful if you want to unlock advanced functionality.
Although many users pick up a quality Chromebook because of the simple browser-based experience, there's much more you can do with it if you're comfortable tweaking more advanced settings. For example, you can join the Beta or Dev channel or enable Chrome Flags to try out new features before they launch. If you're a developer, you can also put your Chromebook into Developer Mode to install applications and gain overall deeper access to the ChromeOS system.

The future of AI is almost certainly going to be models trained for specific tasks, rather than general-purpose LLMs.
Large Language Models (LLMs) are powerful tools, and ChatGPT, Microsoft Copilot, and Google Gemini consistently manage to blow me away. Their capabilities are extensive, but they're not without their faults. Hallucinations are a big problem with LLMs like these, though companies are aware of them and try to stamp them out whereveer possible. However, I don't think these models are the future of LLMs. I think the future of AI are the smaller, specialized models, rather than the general purpose tools that these are.

Google's Gemini 1.5 Pro model wowed us, and the Ultra model could be even better.
There's an ongoing arms race in the artificial intelligence sphere, particularly between big players like OpenAI, Microsoft, and Google. These three companies are locked into a never-ending battle of advancement, and Google is especially an outsider given that it doesn't use OpenAI's GPT technology at all. Google instead has been using its own home-grown technology, initially starting with PaLM and Bard and now more recently switching to Gemini 1.0 and Gemini 1.5. With Gemini 1.5 Pro already seemingly doing the impossible, we've never been more excited for Gemini 1.5 Ultra.