ESET, an Internet security company that offers anti-virus products, just publicly disclosed a vulnerability in Wi-Fi chips made by Broadcom and Cypress. The vulnerability, which ESET calls "Kr00K," allows for the unauthorized decryption of WPA2-encrypted network traffic. Devices with Broadcom and Cypress FullMac Wi-Fi chips, which, according to ESET, are found in the Amazon Echo/Kindle, Apple iPhone/iPad/MacBook, Google Nexus, Samsung Galaxy, Xiaomi Redmi, and more, could be vulnerable. Furthermore, even if a client device has been patched, an attacker can intercept network traffic if the wireless access point or router is unpatched.
Here is a list of client devices that ESET confirmed were vulnerable to Kr00k:
- Amazon Echo 2nd gen
- Amazon Kindle 8th gen
- Apple iPad mini 2
- Apple iPhone 6, 6S, 8, XR
- Apple MacBook Air Retina 13-inch 2018
- Google Nexus 5
- Google Nexus 6
- Google Nexus 6P
- Raspberry Pi 3
- Samsung Galaxy S4 GT-I9505
- Samsung Galaxy S8
- Xiaomi Redmi 3S
And here is a list of wireless routers that ESET confirmed were vulnerable:
- Asus RT-N12
- Huawei B612S-25d
- Huawei EchoLife HG8245H
- Huawei E5577Cs-321
ESET also tested Wi-Fi chips from Qualcomm, Realtek, Ralink, and MediaTek, but were unable to exploit this vulnerability. Since there are too many Wi-Fi chips to test on the market, ESET is working with the Wi-Fi Alliance to develop tools to detect vulnerable devices, and since January 16th, 2020, they're also working with ICASI members to ensure that all possibly affected device manufacturers are aware of Kr00K. The vulnerability was assigned CVE-2019-15126 on August 17th, 2019.
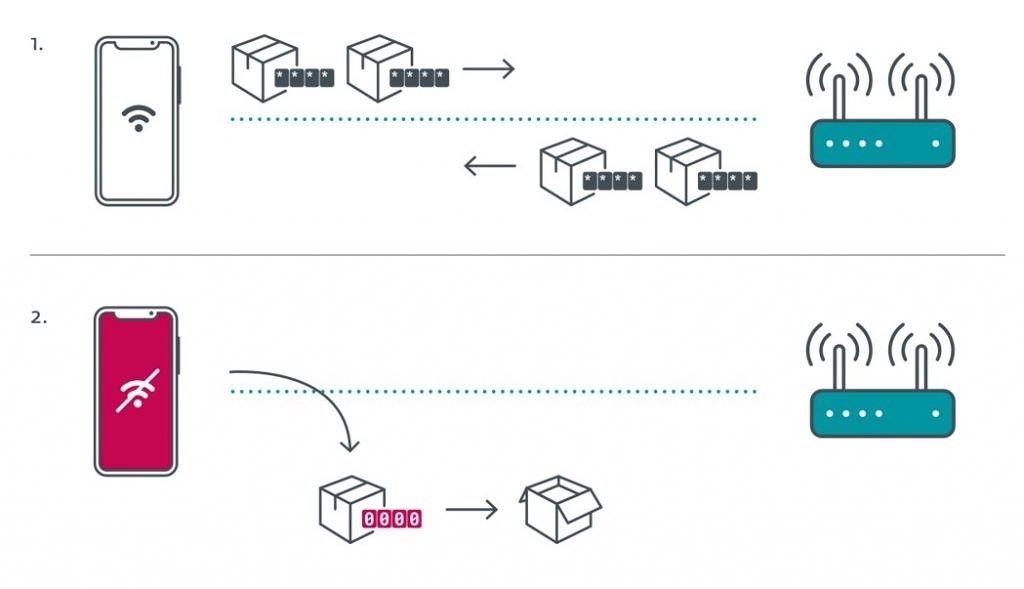
According to ESET, this vulnerability concerns encryption on the Wi-Fi layer and has nothing to do with Transport Layer Security, or TLS. An attack using Kr00k "degrades your security a step towards what you'd have on an open Wi-Fi network." Specifically, the flaw causes vulnerable devices to use an all-zero Temporal Key (TK) to encrypt unicast data frames, which makes it easy for an attacker to decrypt some network packets transmitted by vulnerable devices. The bug occurs after a disassociation between a client device and an access point, which is when an access point re-establishes connection with a client device.
Here is a graphic published by ESET that demonstrates the difference between an unpatched client and a patched client communicating with a wireless access point.
ESET only tested the WPA2-Personal and WPA2-Enterprise protocols with AES-CCMP encryption but did not test whether this vulnerability affects WPA3. Since ESET mentioned the vulnerability affecting Google Nexus devices, we reached out to Google regarding ESET's findings and were given the following statement:
"Pixel devices are not impacted by this vulnerability. Affected Android device manufacturers were notified directly by Broadcom of the vulnerability and the patch." - Google spokesperson
At this time, there's no simple way to check whether your device or wireless access point is vulnerable to Kr00K. To find out if they are vulnerable or have already been fixed, you'll need to reach out to manufacturers. ESET estimates that over a billion Wi-Fi-capable devices and access points could be vulnerable to this exploit, but that patches for devices by major manufacturers have already been released. According to ESET's disclosure timeline, patches have been rolling out since Q4 of 2019. Custom ROM developers will need to wait for OEMs to release updated Wi-Fi binaries; unfortunately, older devices without active support from the OEM will be difficult or impossible to fix. For more information on Kr00K, visit ESET's dedicated webpage.