OnePlus has evolved a lot over the years, and it now has some amazing smartphones in its portfolio to cover different price points. From 2023's flagship OnePlus 11 smartphone to more budget options in the Nord lineup, there are plenty of great OnePlus devices on the market. If you are in the market to buy a new OnePlus phone and are wondering which one to pick, then continue reading to find out the ones I recommend buying right now in 2023. I've handpicked a few OnePlus phones that stand out from the rest and will set you up for at least a few years. Let's dive in and check out the best OnePlus phones you can buy in 2023.
Best OnePlus phones in 2023
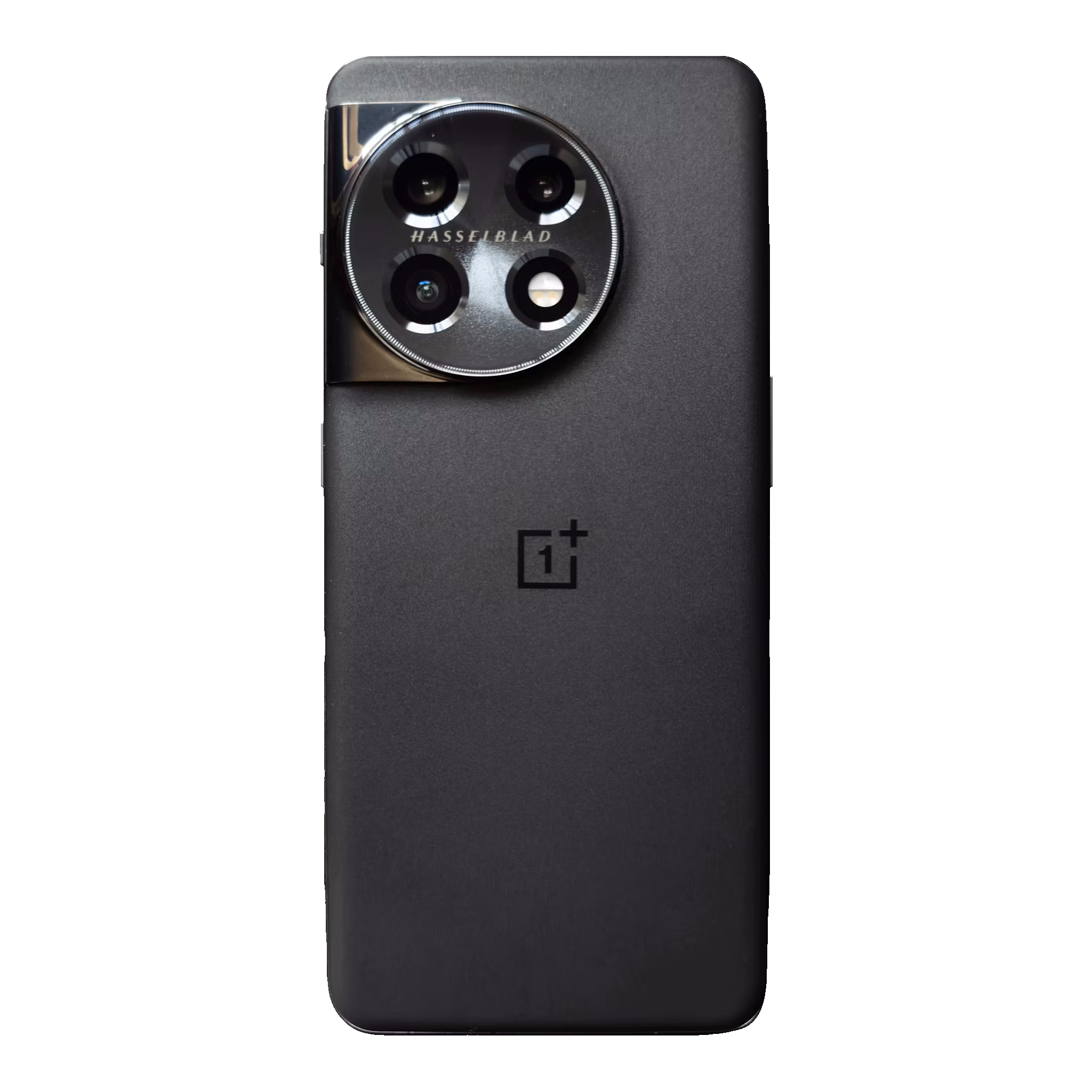
OnePlus 11
The best "flagship-killer' we've had in years
The OnePlus 11 is the company's return to form, offering an almost-flagship experience at a lower price point than what Samsung charges.
- Premium build quality on par with other flagships
- Excellent thermals
- Strong main camera
- Telephoto lens' optical range is short by 2023 standards
- No wireless charging
- Peak brightness is not as bright as other phones
The OnePlus 11 is finally out, and it brings plenty of upgrades over its predecessor, the OnePlus 10 Pro. It's also readily available to purchase in the U.S., which is why it has replaced the OnePlus 10 Pro as the best overall OnePlus phone you can buy right now. One of the highlights of the OnePlus 11 is that it's powered by the new Snapdragon 8 Gen 2 chipset. It's among the first phones to be powered by this particular chip in 2023, so you can expect it to be on par with pretty much all the flagships coming out this year.
OnePlus didn't do a lot to change the overall look and feel of the OnePlus 11, but it is easy to distinguish between the OnePlus 10 Pro and the OnePlus 11 when you look at them from the back. The camera module on this phone is now circular with a more prominent Hasselblad branding. The camera system at the back of the OnePlus 11 includes a 50MP main camera, a 48MP ultrawide, and a 32MP telephoto lens. A 16MP front-facing shooter handles selfies, and they all are capable of capturing high-resolution videos too.
The OnePlus 11 packs the same 5,000mAh battery that we saw in the last year's flagship too, but the new phone now supports faster charging. That's right, the OnePlus 11 units sold in the U.S. support 80W fast charging instead of the 65W charging support we saw on the last year's flagship. The rest of the hardware is also very similar to what we saw on the OnePlus 10 Pro, so it's safe to say that OnePlus has simply improved upon what is already a solid package from last year.

OnePlus 10T
The affordable performance flagship
The OnePlus 10T tries to make up for its compromises with a flagship chipset and super fast charging speeds.
- Super fast charging speed
- Reliable performance
- Affordable than most flagships out there
- Weaker cameras than OnePlus 10 Pro
- No support for wireless charging
The OnePlus 10T is a slightly toned-down version of the OnePlus 10 Pro, which downgrades some things like the display and the overall build quality. You only get a full HD display on the OnePlus 10T instead of a quad HD panel on the OnePlus 10 Pro. It also comes with a plastic frame around the body as opposed to a metallic one on the 10 Pro. OnePlus tries to make up for these things by offering faster charging speeds and a new chipset.
The OnePlus 10T, in case you're wondering, supports 150W charging speeds. It also comes with a bundled charging brick, meaning you don't have to buy one separately. OnePlus promises that the included charging brick can charge the OnePlus 10T from 1% to 100% in just 19 minutes — a bold claim that XDA's Technical Editor Adam was able to confirm during his testing for the review. The US variants of the phone are limited to just 125W charging speed, so keep that in mind.
Another highlight feature of this phone is the new Snapdragon 8 Plus Gen 1 chipset. This particular chipset is an upgraded version of the Snapdragon 8 Gen 1 chip powering the OnePlus 10 Pro. Is it an improvement? Yes, the new chipset is undoubtedly a winner, and you can learn more about it in our Qualcomm Snapdragon 8 Plus Gen 1 vs Qualcomm Snapdragon 8 Gen 1 comparison. The OnePlus 10T is one of the fastest phones you can buy right now, and it delivers impressive speeds on the charging front, too.
What's not so impressive about this phone, however, is the camera performance. The OnePlus 10T takes a massive hit in overall quality by downgrading the sensors. It's not the company's camera flagship, and it's certainly far from the best camera flagship out there on the market in 2023.

OnePlus 10 Pro
Still worth considering with a discount
The OnePlus 10 Pro may not be the latest flagship on the market, but it holds up very well in 2023. The device is powered by a Qualcomm Snapdragon 8 Gen 1 processor, 8GB RAM, and 128GB of internal storage. While it did have a retail price of $899 when it first launched, you can purchase the phone for over 50% off, coming in at just $400 for a limited time.
- Solid performance
- Good battery life
- Reliable set of cameras
- Limited to 65W charging in the US
- No official IP rating
The OnePlus 10 Pro may not be the latest phone from the brand out there, but it still holds up very well and is readily available to buy. One of the main selling points of this phone is the Snapdragon 8 Gen 1 chipset. You're probably buying a OnePlus smartphone because you prioritize good performance over anything else on a phone.
The OnePlus 10 Pro isn't going to win any awards for its design, but it looks unique and is instantly recognizable. The camera island definitely looks a lot busier than what you get on many other phones, so I'll let you decide if it's any good. The cameras themselves hold their own against other phones on the market, but they're far from the top-end flagships. You can check out our OnePlus 10 Pro camera review to learn more about the cameras and also check out some samples.
The Snapdragon 8 Gen 1 chipset ensures the OnePlus 10 Pro delivers reliable performance day in and day out without breaking a sweat. Not only does the Snapdragon 8 Gen 1 chipset delivers the same level of performance as the already powerful Snapdragon 888, but it also leaves enough headroom to generate less heat overall. You can learn more about the phone's performance in our OnePlus 10 Pro review, so be sure to check it out.
The OnePlus 10 Pro also excels in the battery department, thanks to a 5,000 mAh unit. It'll comfortably last you through a day, even with heavy usage. It's no small feat for any smartphone to offer five hours of screen time with heavy usage, especially when you have things like a big and bright high-refresh-rate AMOLED display to power through. What's also impressive is the included 65W charger inside the box with the OnePlus 10 Pro units in the US.

OnePlus Nord N30 5G
Excellent phone for casual users
The OnePlus Nord N30 5G brings the expected fast and smooth experience of a OnePlus phone along with an impressive 108MP camera at a great price.
- Beautiful design
- Fast UI and capable processor
- Affordable price tag
- The cameras could've been better
- Uses same chipset as predecessor
The Nord N30 is OnePlus' latest phone to go against the best budget phones with its $300 price tag. It brings mostly the same experience as last year's Nord N20 as they share a lot of similarities, but I recommend picking up the new phone over its predecessor if you're shopping for a budget phone from OnePlus. I say that because the newer model brings a slew of upgrades that make it better than the Nord N20 for the same price.
One thing I personally like about the OnePlus Nord N30 is that it looks just as good as its predecessor, if not better. My colleague Ben — who reviewed the Nord N30 for XDA — says it feels a bit cheap and plasticky to touch, though. The Nord N30 comes with an LCD panel as opposed to the OLED panel that we saw last year, but the newer one supports a higher refresh rate to be in line with other phones on the market right now.
Another important upgrade to consider is that the Nord N30 features a 108MP main sensor, replacing the older 64MP sensor. The overall camera experience remains largely the same, and they're equally versatile in terms of shooting modes. Some other noteworthy features of the Nord N30 include 8GB of RAM, a 5,000mAh battery with support for up to 50W wired charging, and also a 3.5mm headphone jack.

OnePlus Nord N300 5G
Not bad at all for a free phone if you're ready to lock in
The OnePlus Nord N300 is a 5G-enabled budget phone that's exclusive to T-Mobile and Metro PCS in the U.S., and you can get it for free if you sign up for a two-year plan.
- Free if you commit to a two-year contract with T-Mobile or MetroPCS
- Fast charger with charger included
- Good battery life
- No ultra-ide or zoom lens
The OnePlus Nord N300 5G is also a good option if you're in the market to buy a budget phone. It's very similar to the Nord N200 5G overall, but it does a few things better. It's exclusive to T-Mobile and MetroPCS in the U.S., but you can also get this particular phone for free if you sign up for a two-year plan.
The Nord N300 5G sports a 6.5-inch 720x1612 LCD panel with support for up to 90Hz refresh rate. It peaks at 500 nits brightness, so it gets decently bright and produces vibrant colors. It's no match for the OLED panel that you get on other phones out there, but it'll get the job done. It's powered by the MediaTek 810 chip coupled with 4GB RAM and 64GB internal storage. You get support for a microSD card, so the lack of storage options shouldn't really be an issue.
The OnePlus Nord N300 5G comes with a 5,000mAh battery and support for up to 33W charging speeds. You also get a charger in the box with this phone, so you don't have to spend any additional money on it. You also get a dual camera setup at the back which includes a 48MP main and a 2MP depth sensor.
There's nothing to write home about the Nord N300 5G overall, but it should be enough for all casual users. You can purchase it for $228 with no strings attached, but I only recommend buying it for free from T-Mobile or MetroPCS with a two-year contract. The Nord N200 5G might be worth considering for a cheaper price instead if you don't want to sign up for a contract.

OnePlus Nord 2T
A decent phone at a lower price
The OnePlus Nord 2T is the latest mid-range offering from OnePlus, packing a lot of punch for the price.
- Attractive design
- Reliable performance
- Fast charging support
- Just a minor update over Nord 2
- No official IP rating
The OnePlus Nord 2T improves upon the already excellent Nord 2. It gets all the fundamentals right to deliver a solid mid-ranger for those who don't want to open their wallets for a flagship phone. From the reliable Dimensity 1300 chipset to a beautiful 90Hz AMOLED display, the OnePlus Nord 2T offers a lot of good features to become one of the best Nord phones you can buy right now. It's not available to purchase in the U.S., though, so you'll have to import it from other markets such as the U.K.
The OnePlus Nord 2T may not be the prettiest phone on the market, but it's still better than a lot of other mid-rangers out there. There's a 6.43-inch display on the front with support for a 90Hz refresh rate. It's an FHD+ AMOLED panel, which is what you'd expect to see in the mid-range segment. The phone draws its power from MediaTek's Dimensity 1300 chipset, which is coupled with up to 12GB of RAM and up to 256GB of storage. The Dimensity 1300 is a reliable chipset for all your day-to-day tasks, and it's almost on par with a lot of flagship chips out there.
As for the optics, the OnePlus Nord 2T packs a triple camera setup which includes a 50MP main sensor along with 8MP ultra-wide and 2MP monochrome lenses. I suggest you stop by our OnePlus Nord 2T review to check out both photo and video samples captured from the phone. The device also packs a 4,500mAh battery with support for up to 80W charging out of the box. Overall, the Nord 2T is a fantastic mid-range phone that I wish was available to purchase for economical shoppers in the US.
Best OnePlus phones in 2023: The bottom line
The OnePlus 11 checks a lot of the right boxes to become the best phone in this collection. It looks very similar to the OnePlus 10T and the OnePlus 10 Pro, but it has upgraded internals for superior performance, and it also has a better set of optics to help you capture good photos. There is an argument to be made about it is only a minor upgrade over the OnePlus 10 Pro, but you do get an upgraded package overall with better software support than the OnePlus 10 Pro considering it'll get more updates. So unless you're getting an unmissable deal on the OnePlus 10T or the OnePlus 10 Pro, I recommend sticking with the newer flagship.
I've also added some budget phones to the list, including the Nord N30 5G and the Nord N300 5G, so be sure to explore all the phones before making a purchase decision. If you want to check out what manufacturers offer in the name of competition, then you might want to look up our list of the best Android smartphones and the best Samsung Galaxy smartphones on the market.
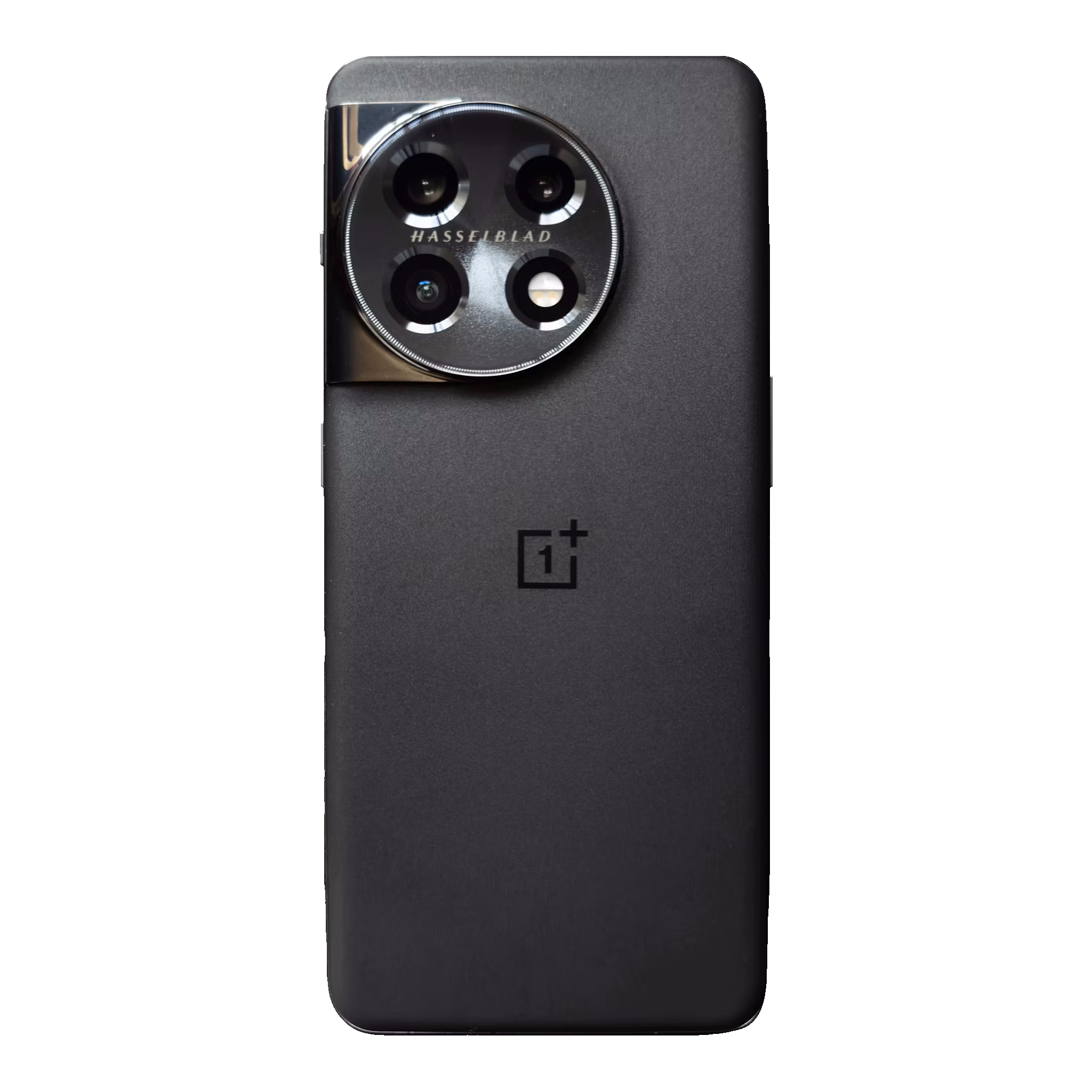
OnePlus 11
The OnePlus 11 is the company's return to form, offering an almost-flagship experience at a lower price point than what Samsung charges.
